If you have an e-commerce or business WordPress site, most probably you’ve already heard of PCI DSS and PCI compliance.
As an online merchant / seller your WordPress website has to be compliant to the PCI DSS regulations, otherwise you risk being fined. Even if you use a third party payment gateway such as PayPal or Stripe, there are still some regulatory requirements your website has to adhere to.
We have prepared this definitive guide to WordPress PCI compliance for site owners to help you build a PCI DSS compliant website. In this guide we explain in detail all you need to know about PCI DSS, PCI compliance and how you can have a PCI compliant WordPress site for your business.
What is PCI DSS and PCI Compliance?
PCI DSS stands for Payment Card Industry Data Security Standard. It is a set of actionable security requirements and regulations online business merchants need must adhere with to be in compliance. The regulations are maintained by the Payment Card Industry Security Standards Council, which is formed by the five major credit card companies: Visa, MasterCard, American Express, Discover and JCB.
Every merchant, regardless of its size, number of transactions it handles and its revenues, falls under PCI.
PCI for WordPress & e-commerce sites
Since most WordPress sites use a third party payment gateway, the scope and requirements are lower. In fact most probably compliance can be achieved by completing the PCI Data Security Standard Self Assessment Questionnaire (SAQ). However you should still inform yourself about the requirements, so whenever you make changes you can determine what is required to remain compliant.
Should I care about PCI Compliance for my WordPress site?
Failing to comply you will face penalties, fines, and may even be barred from accepting credit card payments in the future, not to mention the damage to your business’ reputation and loss of client trust.
Though you should not only care about PCI regulations because of fear mongering. The PCI regulations are good recommendations and help you secure your WordPress e-commerce solution. So by applying them you minimize the risk of having your site hacked and suffering data breaches.
The PCI DSS requirements
The latest version of the PCI DSS regulations is 3.2.1 and it was released in May of 2018. We will update this post whenever the regulations are updated.
The PCI standards are divided into 6 major categories and 12 requirements:
Build and maintain a secure network and systems
- Requirement 1: Install and maintain a firewall configuration to protect cardholder data.
- Requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters.
Protect cardholder data
- Requirement 3: Protect stored cardholder data.
- Requirement 4: Encrypt transmission of cardholder data across open, public networks.
Maintain a vulnerability management program
- Requirement 5: Protect all systems against malware and regularly update anti-virus software or programs.
- Requirement 6: Develop and maintain secure systems and applications.
Implement strong access control measures
- Requirement 7: Restrict access to cardholder data by business need to know.
- Requirement 8: Identify and authenticate access to system components.
- Requirement 9: Restrict physical access to cardholder data.
Regularly monitor and test networks
- Requirement 10: Track and monitor all access to network resources and cardholder data.
- Requirement 11: Regularly test security systems and processes.
Maintain an information security policy
Managing a WordPress PCI compliant site
The above list of requirements might be intimidating to an SMB. However, having a PCI compliant WordPress site and business system is more attainable than you’d think. Most of the regulations are based on best practices and are very easy to implement and adhere to, as this document explains.
PCI DSS requirement 1: Install and maintain a firewall configuration to protect cardholder data
There are many solutions available for WordPress. Most of them do all the hard work for you. For example, if you use a WordPress firewall, you have an out of the box compliant configuration.
Though WordPress PCI compliance is not just about your website. It covers every aspect of your business’ IT and physical security. So apart from configuring a firewall for your WordPress site you should also think of configuring and using a firewall for your office and home networks. The PCI DSS also requires every user that accesses cardholder data to have a personal firewall on their computer.
So if for example you have a WiFi internet router at home, check its configuration and configure the firewall. If you want to access cardholder data directly from your laptop, if you do not have a personal firewall then use a Jump server configuration (connect to a more secure server through which you can access the data).
Best practices & recommendations for configuring firewalls
Here are some security best practises you should keep in mind for when configuring firewalls:
- Keep a list of every server, network devise and service that makes part of your website and IT setup. Write down what each is used for and where it is allowed to connect, and from where it can be accessed. Such documentation helps you determine where you need firewalls and how to configure them.
- When configuring a firewall block both incoming and outgoing. Then only allow what is needed. This sounds like a restrictive policy though it is by far the most effective. For example if you configured a rule by mistake, there will always be the deny-all rule to catch any unwanted traffic.
- If you are suspicious about giving access to a service or a user, or you’re unsure what type of access is required, always do your own research to find out what is actually required, thus avoiding opening unnecessary access.
- Document all the firewall configurations and keep the documentation up to date. If you use a firewall such as iptables it is very easy to document the config, since it is a text file so just keep a copy of the config.
PCI DSS requirement 2: Do not use vendor-supplied defaults for system passwords and other security parameters
Starting with passwords; always change default passwords and enforce policies for stronger WordPress security. The same applies to default software installations and configurations. Here are a few things you should think of when addressing this requirement:
Processes isolation
If the budget permits you should have a segregated server or use a different online service for different roles, such as the database server, web server, DNS server etc. Avoid the web hosts’ recommendations to host everything with them, including the domain, DNS, emails and website. This is against the requirement and by doing so your site and business operations won’t be compliant.
When setting up your site, or renewing your existing services think of segregation. It is possible to segregate services and roles without spending a lot more. You won’t have a dedicated server for every role but you can:
- Buy and host your domain from Registrar A.
- Setup your domain’s DNS nameservers with a DNS provider B.
- Host your website with web host C.
- Your testing and staging environment should be hosted with a different web host D, or on a different server.
- Use an online email services from email provider E.
The more you grow the more you can justify segregation. You might miss on some special offer package because of segregation, and it will cost a bit more, but it is certainly the way to go if you want a secure and compliant WordPress e-commerce site.
Use the least possible services & minimal installations
From the WordPress security point of view, this means that you should:
- Only install plugins and components that you trust and use (learn how to choose the right WordPress plugin).
- Remove all disabled plugins, unused themes and custom code.
- Disable any functionality in plugins and themes that you do not require.
Apply the same ideology to your web server, web host account and any other service you run. For example a default dedicated server has a Web, FTP, SSH, SMTP, DNS, IMAP and other services. Hosting accounts typically have applications such as phpMyAdmin and CPanel. If you use SSH only to configure your server disable the services you do not need.
Start with a bare installation
If you are installing new software or setting up a new server start with a minimal installation. Only activate what you need. The same concept applies to web hosts – many provide a lot of functionality, such as their own email servers that many do not use. Ask for the most basic account and then enable the features you need.
Harden your plugins, service & software
Once you have installed all the services and applications for your WordPress site and business, it is time to configure them. Refer to vendors’ hardening guides and best practices recommended on the internet to secure your web server, the operating system and any other service you have running on your web server.
PCI DSS requirement 3: Protect cardholder data
If you use an e-commerce solution like WooCommerce or Easy Digital Downloads to power your e-commerce WordPress site most probably you use a third party payment gateway such as PayPal or Stripe to process online payments and handle cardholder data. So as such this requirement might not apply to your WordPress site.
However, in case of exceptions such as payments are processed manually, or there is a data entry process to complete the order it is of utmost importance to know what the regulations in this requirement are, to ensure the process is compliant:
- Never write down cardholder data information. Only input data directly in the payment gateway.
- Only store the cardholder data that you need, even if you are using a third party payment gateway.
- Delete the cardholder data that you no longer require and implement data retention policies.
- Educate the personnel that handle cardholder data about the best practices when manageming passwords. Make sure they know how they should handle the sensitive information.
PCI DSS requirement 4: Encrypt transmission of cardholder data across open, public networks
The best way to adhere to PCI DSS requirement 4 is to install and use a certificate for your WordPress site, so it is accessible over HTTPS. With a certificate all communication between the visitors and your website is encrypted. For more information on certificates refer to WordPress HTTPS and SSL/TLS certificates.
If your site is still not on HTTPS you can set it up within a few minutes. Many web hosts provide free SSL/TLS certificates via Let’s Encrypt, a free, automated and open certificate authority. So there is no excuse to not having your WordPress site on HTTPS.
Should you need to access cardholder data on your payment gateway access it via secure means. Even if you access it over HTTPS, make sure to take the necessary precautions, if for example you are connected to a public WiFi. In such case you should always use a VPN connection.
PCI DSS requirement 5: Protect all systems against malware and regularly update anti-virus software or programs
This requirement focuses on maintaining a vulnerability management program so systems are not vulnerable to specific attacks and well protected against any type of malware threat. This means ensuring that all anti-virus and other protection software is up to date and is actively scanning the systems.
Most WordPress firewall solutions also have malware scanning capabilities. So by using one of them on your site you are also complying to this requirement.
As for the rest of the business network and the computers used to access the WordPress site and payments gateways, use a solution that can help you:
- Setup a strong password – the laptop / computer should always be locked when not in use
- Encrypt data – both Windows and Mac operating systems have built-in utilities to encrypt the drives
- Has Updated malware and anti-virus software that periodically scans the computer
- Uses a personal firewall that can block malicious traffic and with which you can see outgoing connections. There are quite a few third party solutions available on the market that do not cost much. Also, Windows also have a built-in firewall.
The above applies to any device you use to do any type of business transaction. So if you check your emails or access your WordPress admin pages from your smartphone or tablet, they should also be locked down.
Use a VPN connection
If you work from different remote locations, use a personal VPN software. As a security precaution I would recommend you to always use VPN when working remotely, even when not using public WiFi networks.
PCI DSS requirement 6: Develop and maintain secure systems and applications
Requirement 6 of the PCI Data Security Standard addresses two different but related problems:
- Maintain all the software and applications you use and ensure they are secure,
- Ensure the applications and software you develop an use are developed securely and do not contain any vulnerabilities.
In this article we will focus on the former, because the latter applies to developers and explains how to avoid vulnerabilities such as SQL Injection and Cross-site Scripting in applications.
Maintaining existing application secure
Let’s start with the software and applications you already use. Always install the hot fixes and updates the vendor releases in a timely fashion. Since updates are critical, when choosing a new software make sure it is:
- Developed by a responsive vendor.
- Frequently updated and the vendor addresses bugs and reported security issues in a timely manner.
- Licensed to ensure you receive all the security patches and updates.
Introducing new applications in your business and processes
As your business and WordPress e-commerce site grow and change you will need to use new software, online services, scripts or WordPress plugins. Whenever you need to do so:
- Research the solution and read the reviews to see what other users say about it.
- Once installed change all the default settings and passwords.
- Follow the security guidelines and vendor’s best practices to configure and use the solution securely.
- Subscribe to the vendors security newsletter or update service.
Maintaining the vulnerability management program
There are several approaches you can take for effective vulnerability management. However it depends on the type of web host, operating systems and devices you use.
In case of WordPress, most hosting providers manage all the WordPress patch management for you. They also alert you if you are running a plugin or theme with a known vulnerability. As an extra precautionary step, you should also:
- Install a WordPress activity log plugin to keep a log of changes and detect file changes on your WordPress site.
- Add an extra layer of security in front of your WordPress site with a web application firewall (WAF) such as Sucuri or Malcare.
PCI DSS requirement 7: Restrict access to cardholder data by business need to know
On your site you can use the WordPress user roles to manage users’ privileges. Should you need you can use third party plugins to create custom roles and further fine tune the privileges.
Also, check and limit the access of all the users on all systems, including the servers’ operating systems, all the online services and network components, such as firewalls, switches and routers.
The easiest way to implement a rock solid access control system is to use the deny all and principle of least privileges methods. Start by denying access to everyone, and only assign the privileges users needs. Do not give admin access to a WordPress site or a network component to someone to save a few minutes of work. Research and learn what access every user needs to the WordPress site, MySQL database, NAS or any other device.
PCI DSS requirement 8: Identify and authenticate access to system components
This requirement focuses on authentication methods and authenticated access. In short, users should always be authenticated when accessing sensitive information such as cardholder data.
Authentication & methods
All sensitive business data, administrator consoles, users account pages and other point of entry should be protected with strong authentication mechanisms. If can setup two-factor authentication (2FA), do so. Here is a round up of the best two-factor authentication WordPress plugins which you can use to set up 2FA on your site or multisite network.
Use unique credentials
Every individual who requires access to your WordPress site, admin portals, customer portals, network devices and business data, including cardholder data, should have unique credentials. This is very important otherwise you won’t be able to track back user activity in the activity log.
Also, credentials should never be shared because they lead to a number of security issues and encourage the use of easy passwords.
Educate your users to use strong passwords
Educate your users to use strong passwords, even if you implemented 2FA. You can educate your users by:
- Configuring policies to force WordPress users to use strong password
- Explain to them what are the repercussions of using weak passwords
- Show them how to use a password manager such as KeePass
Review existing infrastructure
Implement security policies to ensure that all the IT infrastructure components, including your WordPress site are working and secure. Every few months check the existing IT infrastructure and confirm the policies are being applied, thus ensuring that sensitive business and cardholder data is secure.
PCI DSS requirement 9: Restrict physical access to cardholder data
This requirement is fairly straightforward – restrict physical access to your servers, business laptops and smartphones only to those who need access. There are several means and ways how you can do this, and it all depends on the size of the setup that you have.
Here are a few high level tips which can help you get started with requirement 9 of the PCI DSS:
- Restrict access to your network – do not expose network jacks and password protect all WiFi networks,
- Do not allow visitors or any unauthorized personnel to roam free in the office building,
- Always lock unattended laptops, computers, servers and portable devices such as smart phones,
- Destroy any physical evidence of cardholder data.
Even a piece of paper could be evidence, so always shred the paper you do not need. The same with hardware that stores sensitive data. Data should always be encrypted, and if the hardware is no longer required it should be destroyed.
PCI DSS requirement 10: Track and monitor all access to network resources and cardholder data
This PCI DSS requirement 10 requires you to retain audit trail history for at least one year, with a minimum of three months immediately available for analysis.
Note: This section about requirement 10 is a summary. To learn more about the topic of logs in PCI DSS compliance read PCI DSS Requirement 10 for WordPress.
Activity logs, audit trail, security logs or simply logs, are all essential to better manage and keep your IT infrastructure, web farm and WordPress sites secure. You should implement them not just because of PCI DSS, but because logs allow you to see what happened on your WordPress and learn about the attacker so you can better protect your setup.
Every network device such as switches and routers, and network services such as SMTP and the Apache web server, have logging capabilities. So whenever you set up a new device, service, or install a new software that has logging capabilities enable them.
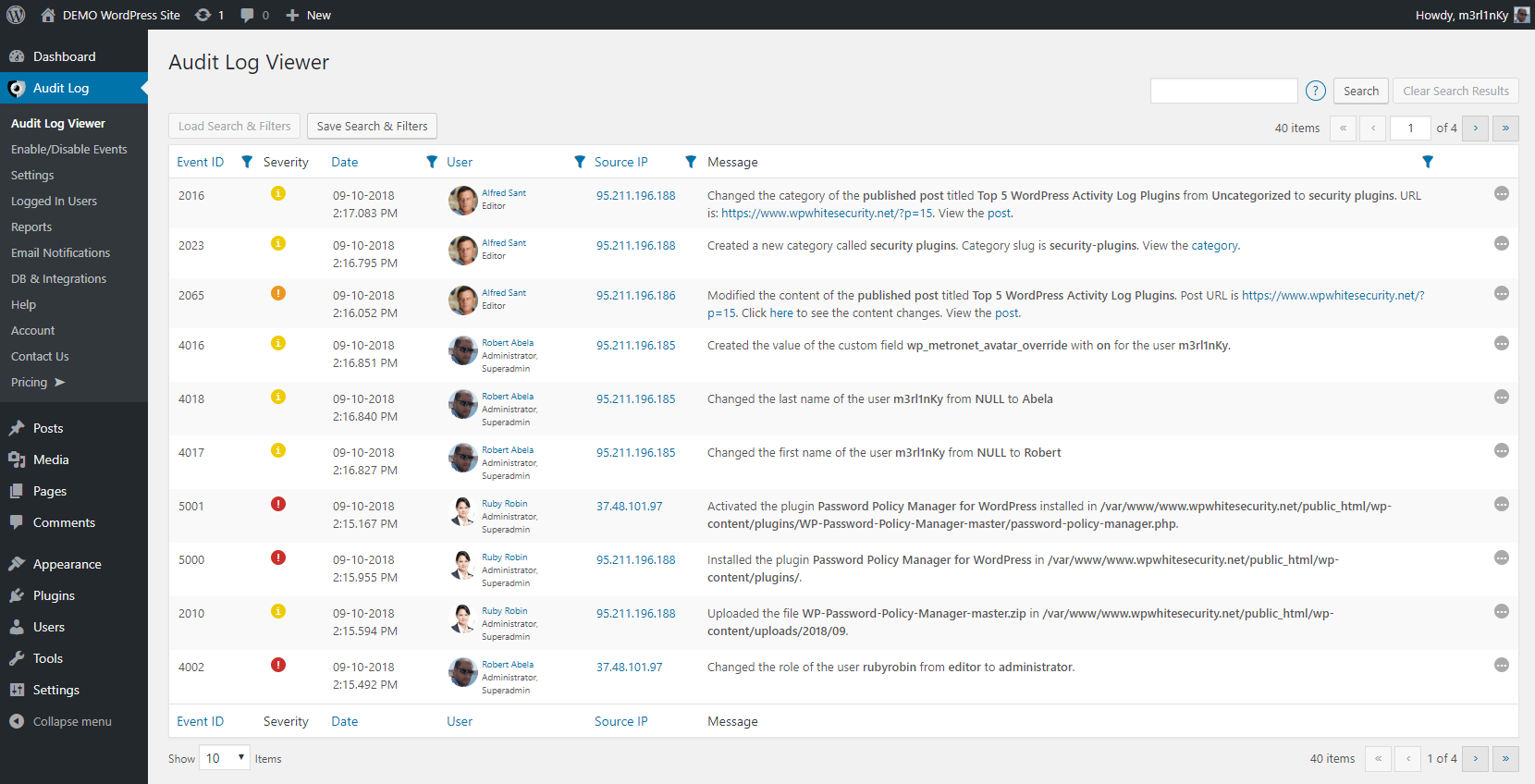
For your WordPress sites we develop and recommend WP Activity Log, the most comprehensive activity log WordPress plugin. The plugin fully supports WordPress multisite networks and is also an activity log plugin for WooCommerce.
PCI DSS requirement 11: Regularly test security systems and processes
IT and WordPress security are not one time fixes, but continuous processes. In fact hardening your IT systems and WordPress sites is just one part of the game. You also need to keep them secure for as long as they are online.
So you need to regularly test your systems and processes by running frequent:
- Penetration tests on your network, web servers etc,
- Perimeter network scans,
- Internal security / vulnerability scans and security audits on your internal networks,
- WordPress vulnerability scans with tools such as WPScan on all your WordPress sites.
Use tools to detect & prevent intrusions
To meet this requirement you should also run an IDS or IPS solution that allows you to detect and prevent possible intrusions. There are several solutions available, with Snort being one of the most popular open source network IPS solution.
As a WordPress intrusion Detection System (IDS) use our plugin WP Activity Log.
Tip: Keep an IT infrastructure & web server inventory
Without an inventory it is very easy to lose track of what is running in your environment, resulting in unpatched and insecure software that can be easily exploited by malicious hackers.
In fact one of the biggest challenges enterprises face before securing their web assets is not knowing what they have. So keep an inventory of every device you have on your network, and every software and network service you have running on your sites so you can easily keep track of what needs to be:
- updated and secured
- deleted
An inventory also helps in identifying possible new unauthorized equipment, software, service or WiFi network in the building.
PCI DSS requirement 12: Maintain a policy that addresses information security for all personnel
This is the least technical of the requirements, yet the most difficult to comply with. This requirement focuses on documentation, procedures, and implementing and enforcing policies. Here is a breakdown of how you can comply to this requirement:
- Establish, publish, maintain and disseminate a security policy,
- Implement a risk-assessment process to identify critical assets, threats and vulnerabilities,
- Develop policies to define proper use of technologies such as remote access and hardware,
- Ensure that the security policies clearly define the responsibilities for all personnel,
- Assign security management responsibilities to individuals or teams,
- Implement a security awareness program to educate and raise awareness with your colleagues,
- Maintain a list of all service provides your business uses, including online services,
- Implement an incident response plan.
This requirement might sound like an overkill for small businesses with a few employees. Granted, it applies mostly to large businesses. However do not underestimate the importance of policies and enforcement. It is crucial to start taking care of the basics so when the business grows it won’t be a problem to adapt to the changes and keeping it secure.



